CMMC Level 1 Isn’t Hard
But Most Companies Still Get It Wrong
Part of the rewards that often come from working with the Department of War has to do with the amazing steps and hoops you must pass through in order to do business with this extraordinary organization.
The world’s largest bureaucracy is not for the faint-of-heart.
What CMMC Actually Is
CMMC Level 1 Self Assessment is based on FAR 52.204-21: Basic Safeguarding of Covered Contractor Information Systems. The gist of this FAR is basically this line:
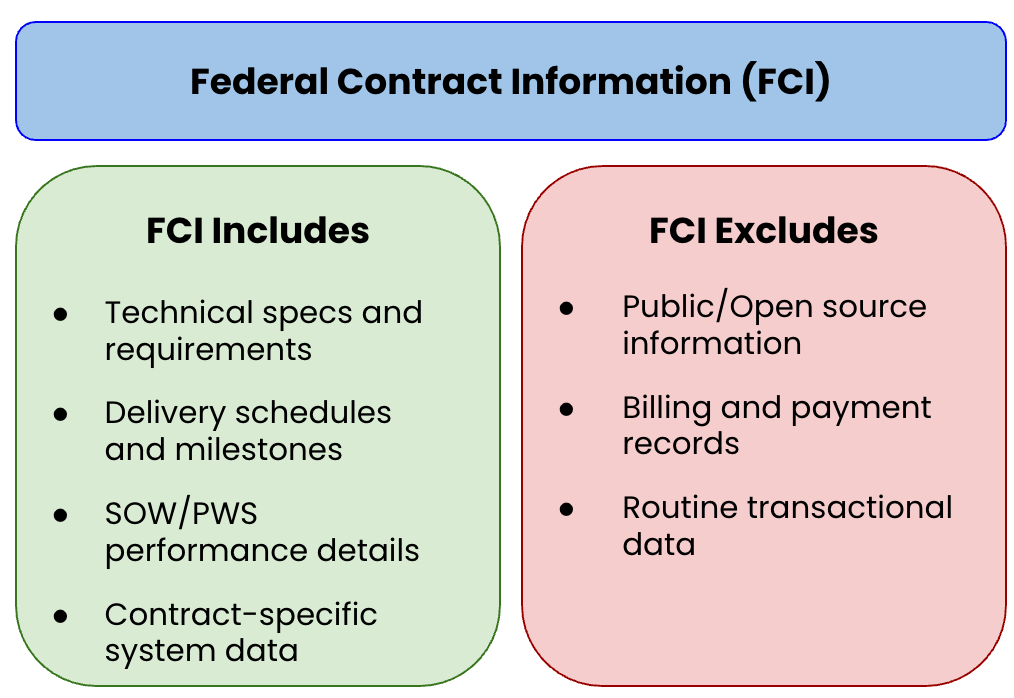
Federal contract information means information, not intended for public release, that is provided by or generated for the Government under a contract to develop or deliver a product or service to the Government, but not including information provided by the Government to the public (such as on public websites) or simple transactional information, such as necessary to process payments.
Basically, if you are touching federal contracts, you are touching FCI. And, you need to do you CMMC Level 1 self-certification. But, you don’t need to pay someone for it (thank goodness).
There are 17 controls in the CMMC Level 1 Self Assessment Guide, spread across 6 categories:
Access Control (AC)
Identification Authentication (IA)
Media Protection (MP)
Physical Protection (PE)
Systems and Communications Protection (SC)
System and Information Integrity (SI)
These are foundational controls, things like: limiting system access to authorized users, using strong passwords, and sanitizing media before disposal. If you are an optimist, you would say that this provides a level of rigor and maturity that will help your company in other aspects of your business. Otherwise, this is just another painful hoop you have to jump through.
There is a scoring methodology here that is a good reference as you work your way through this process.
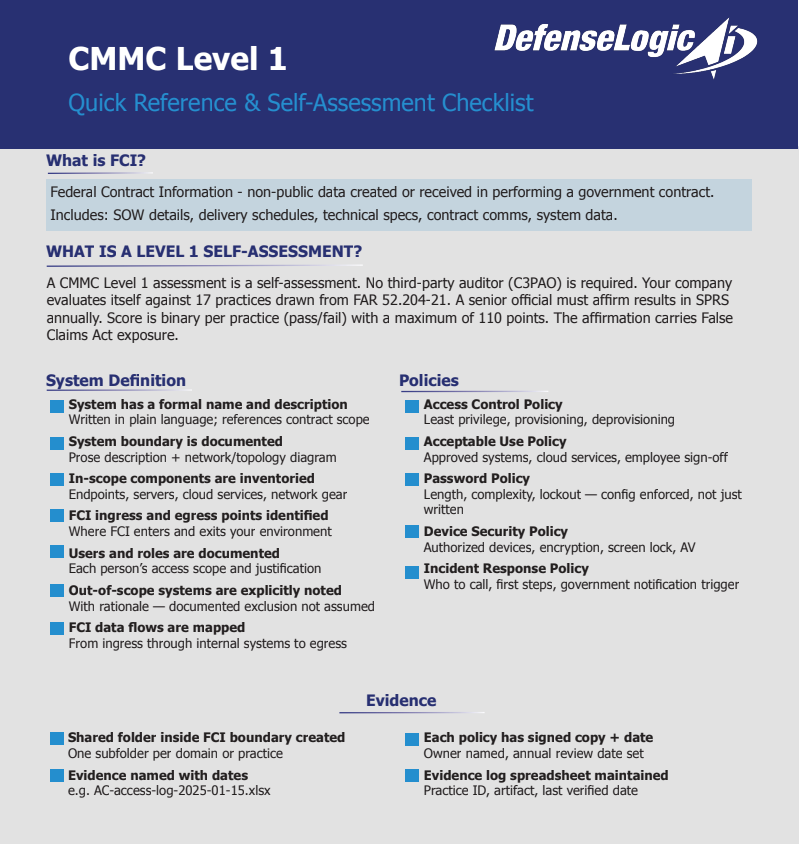
What is a Self-Assessment
A CMMC Level 1 assessment is a self-assessment. This means no third-party auditor is required. Your company evaluates itself against 17 practices drawn from FAR 52.204-21, all focused on basic safeguarding of FCI.
To complete the assessment, a senior company official (typically your CEO or CISO or the person most willing to take on the responsibility) must affirm the results in the Supplier Performance Risk System (SPRS) and assign a score.
Wait….The SPRS? Why yes! Where can you find the SPRS you may ask? I will cover that a bit further down in The Hidden Friction of PIEE and SPRS. So don’t despair!
The score is binary per practice: you either meet it or you don’t, giving a maximum of 110 points. You also have to reassess annually and after any significant change to your environment. I have a little reminder for August of each year to review my assessment and reassess where things are.
The key things that trip contractors up: the affirmation requirement carries legal weight (False Claims Act exposure if you misrepresent compliance), and “self-assessment” doesn’t mean informal: you need documented evidence that each practice is actually implemented, not just assumed.
As always — do NOT free-lance and hope Uncle Sam accepts vibes.
Companies who shortcut requirements will result in more (expensive!!) requirements for third party verifications. Plus, you and your company will likely be barred from doing business with the Federal Government.
Violators do not need to have specific intent to defraud, but must act with "actual knowledge," "deliberate ignorance," or "reckless disregard" of the truth.
What CMMC Is NOT
CMMC Level 1 Self-Certification is not NIST 800-171. This took me a minute to figure this out and I will be writing about this in my next post. NIST 800-171 involves 110 controls and opens up access to some CUI contracts (if you self-certify).
CMMC is not a scored system.
So far, CMMC is not an audit (yet). There is a whole other discussion about the costs of these audits and how it can preclude small businesses from accessing federal contracting opportunities. That is something I will save for another post as well.
The Real Work and Where People Get Stuck
While CMMC Level 1 Self Assessment does not require a formal System Security Plan (SSP) — unlike the NIST requirements — I am a bit of a documentation junkie and believe that if you WRITE IT DOWN, it will be A LOT easier to maintain compliance going forward and to advance into different levels of security certification.
Policies: keep them lightweight
You don’t need a 50-page binder. You need five short documents that tell your team what the rules are and give an assessor something to point at. Each one should fit on a single page. If it’s longer than that, you’re writing a manual, not a policy.
For each policy: name a document owner, set a review date (annually is fine), and get a signature from whoever runs the company. That signature is what makes it a policy rather than a suggestion. If you’re a one-person shop, then you are all of those roles.
Access Control Policy
Covers who can access systems that touch FCI, how access is requested and approved, and what happens when someone leaves or changes roles. The core statement to capture: access is granted on a least-privilege basis, approved by a named authority, and revoked immediately upon departure or role change.
Keep as evidence: the signed policy document, your access approval log (even a simple spreadsheet), and records of any access removals with dates.
Acceptable Use Policy
Covers what employees can and can’t do on company systems — including whether personal use is permitted, what cloud services are approved for FCI, and the prohibition on transferring FCI to unauthorized systems or personal accounts. This is the document that establishes that your employees knew the rules.
Keep as evidence: the signed policy document and acknowledgment records showing each employee (and relevant subcontractors) reviewed and signed it.
Password Policy
Covers minimum password length, complexity requirements, prohibition on password sharing, and lockout thresholds. If you have MFA enforced, note that here too — it strengthens your posture and is worth documenting even though Level 1 doesn’t mandate it.
Keep as evidence: the signed policy document and screenshots or configuration exports from your identity provider or systems showing the policy is actually enforced technically, not just on paper.
Device Security Policy
Covers which devices are authorized to access FCI (company-managed only, or BYOD with conditions), required security configurations (screen lock, encryption, antivirus), and what employees must do before a device is used for contract work. If your boundary includes remote or home-office work, this policy is where you establish the baseline.
Keep as evidence: the signed policy document and a device inventory showing each in-scope device, its owner, and confirmation that required configurations are in place.
Basic Incident Response Policy
Covers how your company identifies, contains, and reports a security incident — including who is responsible, what qualifies as a reportable incident, and your obligation to notify the government if FCI is involved. It doesn’t need to be elaborate. It needs to answer: who do employees call, what do they do first, and who makes the call to notify the contracting officer.
Keep as evidence: the signed policy document, a contact list for the response team, and records of any incidents or tabletop exercises conducted.
Tracking your evidence
The simplest approach that actually works: a shared folder (in whatever document system is inside your FCI boundary) with one subfolder per policy. Inside each subfolder, keep the current signed policy, any prior versions, and a running log of evidence artifacts — named with dates so you can demonstrate currency.
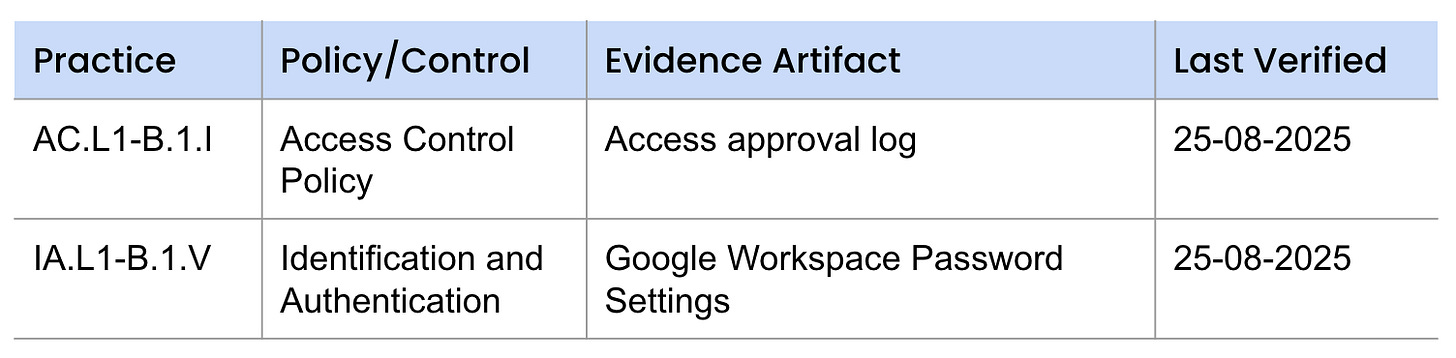
A basic evidence log doesn’t need to be sophisticated. A spreadsheet with four columns gets you most of the way there:
Remember: there are 17 controls in the DODCIO CMMC Level 1 Self-Assessment guide. You should have a line item for each control to keep track of where all this is located and to stay compliant.
The Hidden Friction (SPRS + PIEE)
When I started my own journey of CMMC self-certification (and then NIST 800-171 self-certification), I spent a lot of time getting to know the systems. This begins with the PIEE system. I want to share some of my learnings so that maybe you can reduce some of the headaches that I experienced.
New Vendor Set Up
I am going to assume that your company has a compliant, up-to-date UEI and CAGE code set up in SAM.gov. If you do not, then you should start there and then tackle this step after.
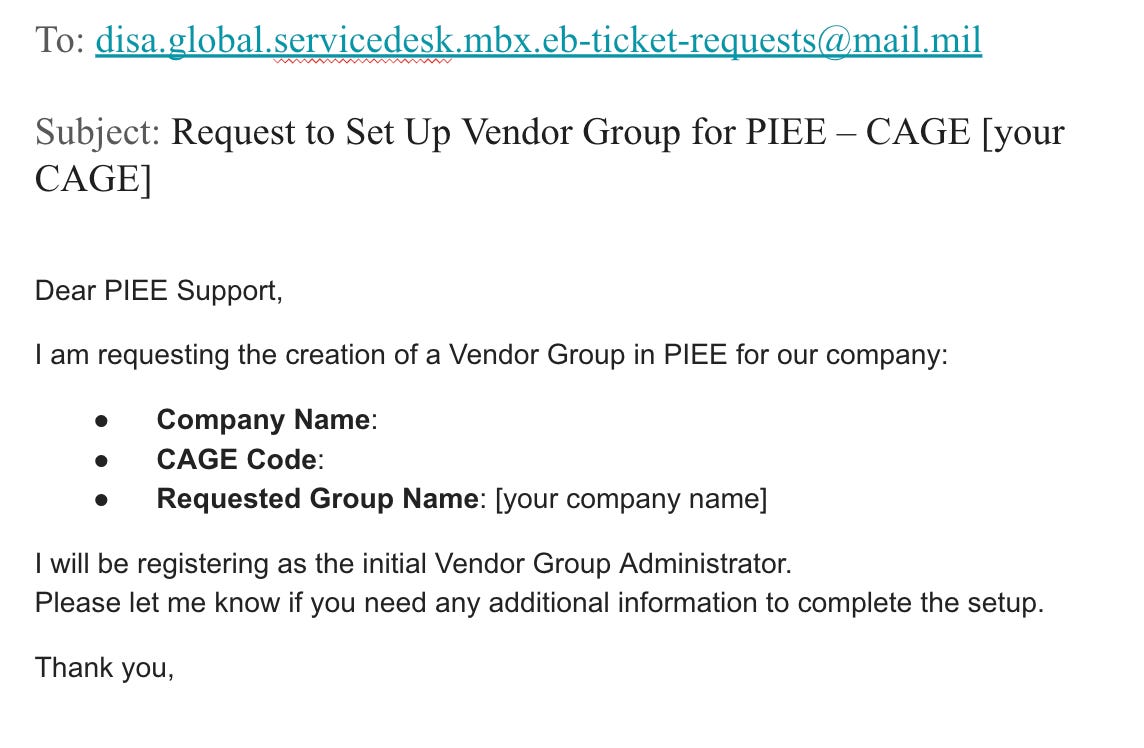
The PIEE has a pretty good help document that can be found here. The first step is to request to set up a vendor group. Here is pretty much what that email looked like for me:
I received a username and an account a few days after this email. They were actually quite responsive (this was in August 2025, so I would be curious to know if folks are seeing issues today).
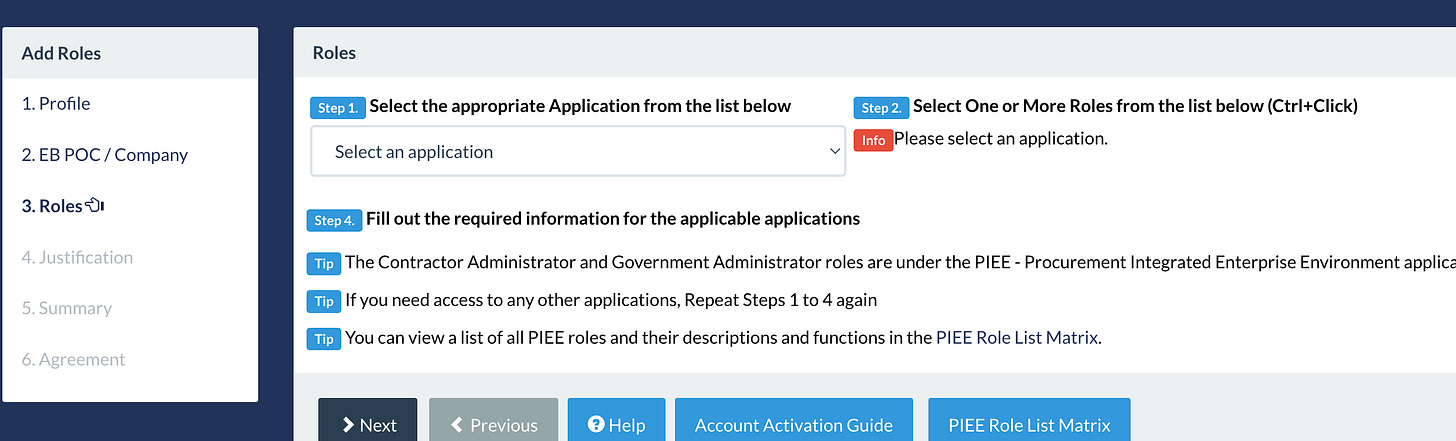
After you receive your account activation, then you must request a role. To do that go to My Account → Request Roles. You will get to a screen that has a drop down where you can request SPRS. Then you will provide justification. Your justification can be as simple as: “User requires access to SPRS to submit CMMC Level 1 self-assessment for [Company Name].”
The vendor admin will need to approve the role request. In many cases, that may be the same person.
SPRS Submission
Then you will get a tile that looks like this.
In SPRS, click on RUN CYBER REPORTS (CMMC & NIST). Then you select your vendor hierarchy and click “add new CMMC Level 1 Self Assessment”.
For Level 1:
Assessment Type: Basic / Level 1 Self
Score: 17 (if fully compliant)
Assessment Date: date completed
Scope/System Description: short description (1–2 lines)
Example: “Company email and endpoint devices supporting federal contract work”
Take a screenshot of this. You never know: PIEE is notoriously finicky.
Once you submit your Level 1 self-assessment in SPRS and confirm the record is saved, you’ve completed the formal requirement.
However, you’re responsible for maintaining those controls and may need to reaffirm annually depending on your contract.
CMMC Level 1 is the floor, not the finish line, but it’s the floor you have to be standing on before any of the rest of it matters. The self-assessment guide gives you the framework. What this post gives you is a starting point for the documentation and evidence that make that affirmation honest.
The SPRS affirmation is a legal commitment. Treat the work behind it accordingly.
Are you looking for a downloadable checklist to help you keep track of your progress? I have created one here that you can download.
In the next post, I will discuss the importance of the DD2345 and NIST requirements, so I hope you will subscribe to learn more!